For organisations operating critical infrastructure and large public sector estates, perimeter security presents a unique challenge. Sites such as transport hubs, utilities, healthcare facilities and government buildings must remain open, accessible and operational, while also protecting against increasingly sophisticated threats. The focus is shifting from static defences to intelligent, risk-based perimeter design that balances security with operational reality…
The complexity of modern estates
Critical infrastructure sites are rarely simple environments. They often feature:
- Multiple access points for staff, contractors and the public
- Large, sometimes remote perimeters
- Mixed-use zones with varying risk levels
- High dependency on uninterrupted operations
This makes a one-size-fits-all approach ineffective. Instead, organisations must design layered security strategies tailored to different areas and threat profiles.
Moving to layered, risk-based protection
Effective perimeter security now relies on a defence-in-depth approach, combining physical, technological and procedural controls.
This may include:
- Physical barriers such as fencing, gates and bollards
- Detection systems including CCTV, thermal imaging and intrusion sensors
- Access control measures for vehicles and pedestrians
Crucially, these elements must be aligned to the specific risks of each zone: for example, stricter controls around sensitive assets, with more flexible access in public-facing areas.
Balancing security with accessibility
Public sector estates, in particular, must maintain safe and welcoming environments. Overly restrictive measures can disrupt operations, create bottlenecks or negatively impact user experience.
Design considerations should include:
- Smooth flow of people and vehicles
- Clear signage and wayfinding
- Minimising friction at entry points
The goal is to integrate security seamlessly into the environment, rather than creating visible barriers that hinder access.
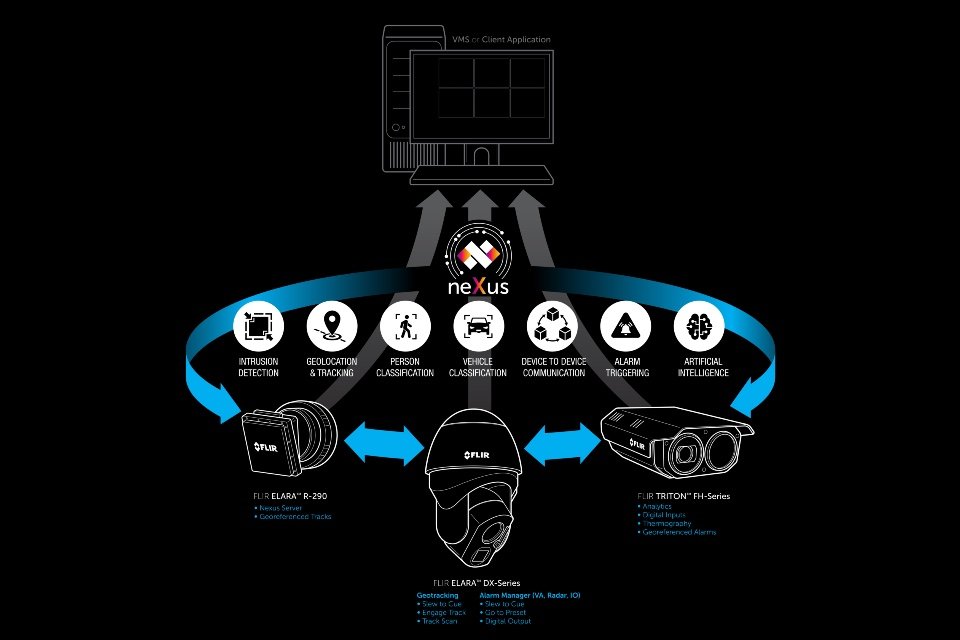
Leveraging technology for early detection
Advances in technology are enabling earlier and more accurate threat detection. AI-driven video analytics, for example, can distinguish between normal activity and potential intrusions, reducing false alarms.
Thermal imaging and radar-based systems can also provide 24/7 monitoring, particularly in low-light or remote areas.
These tools allow security teams to respond proactively, rather than reacting after a breach has occurred.
Integration with wider security operations
Perimeter security cannot operate in isolation. Integration with control rooms, access control systems and incident response processes is essential to ensure alerts lead to effective action.
This includes:
- Real-time alerting and escalation protocols
- Clear communication between on-site teams and monitoring centres
- Defined response procedures for different threat scenarios
Working with the right partners
Given the complexity of critical infrastructure, selecting the right suppliers is key. Organisations should look for partners that offer:
- Experience in similar high-risk, large-scale environments
- End-to-end solutions covering design, installation and ongoing support
- Strong integration capabilities with existing systems
- Compliance with relevant UK standards and regulations
Securing without compromising operations
For physical security leaders, the challenge is to protect assets and people without disrupting essential services.
By adopting a layered, intelligence-led approach (supported by the right technology and partners) organisations can design perimeter security that is both robust and adaptable, meeting the demands of complex estates in an increasingly uncertain threat landscape.
Are you searching for Perimeter Security solutions for your organisation? The Total Security Summit can help!