By Martin Hodgson, Head of UK & Ireland, Paessler AG
The basic tenants of security systems have remained relatively unchanged for the better part of the last few decades. Intrusion detectors, alarm triggers and surveillance systems work in synergy to protect homes and businesses. Nonetheless, in the past few years we have seen security systems become increasingly digitised. Whilst this is not without its benefits such as, remote access for security personnel and alerts sent off site, digitisation has meant that modern security is more reliant on IT networks for success than ever before.
Blurring the lines between physical and virtual
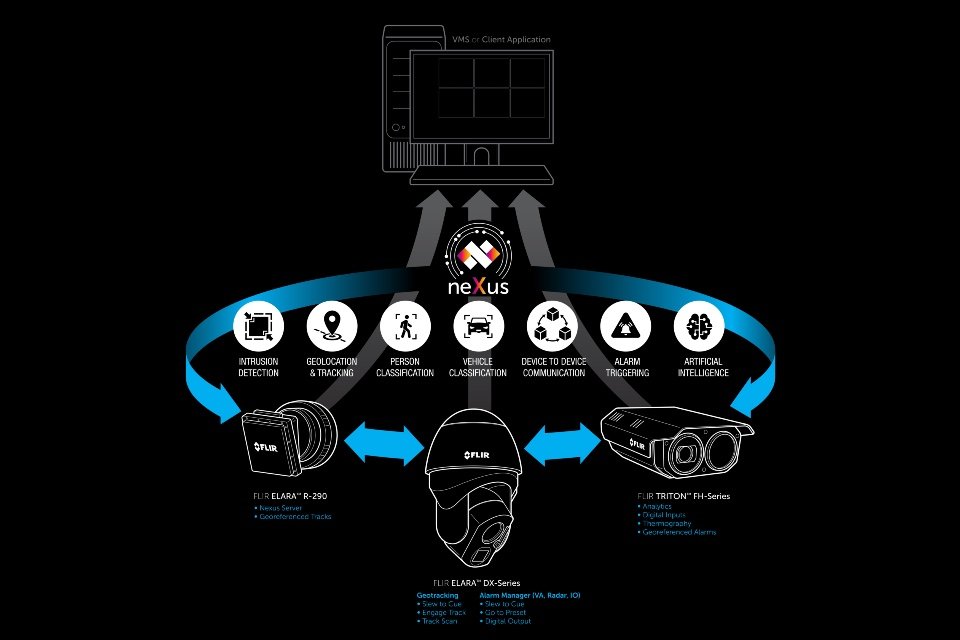
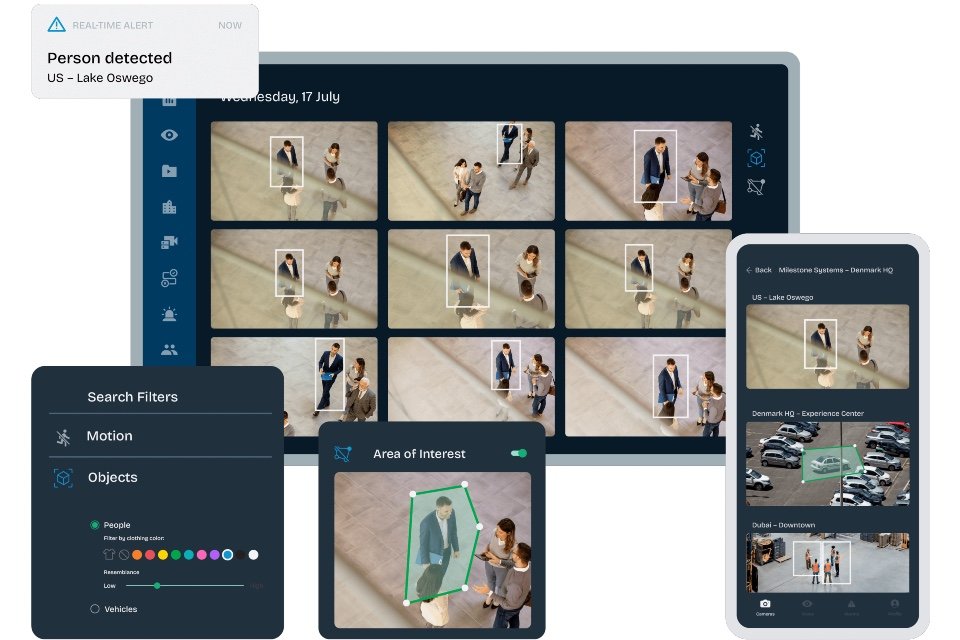
Today, many security solutions are connected to the internet as a part of the Internet of Things (IoT). Solutions such as modern CCTV systems will record and monitor footage using IP cameras, which allows security personnel to wirelessly view footage via a connected device without the need for cables or now defunct analogue video signals. This means security footage can be stored on hard drives or even in a private cloud where user access privileges for cameras and stored footage are secured by an IP access controller. However, it is not just CCTV that is digitised, everything from panic buttons to intrusion detectors are now network enabled.
Digitisation of security systems has come as an immense benefit for security staff. Personnel are now able to monitor and secure facilities without the need for a physical presence on site. Likewise, IoT allows for an incredibly high degree of customisability, making it easier and cheaper to build bespoke security systems for each installation.
New points of failure
Nonetheless, that’s not to say digitisation and IoT network enablement of security systems haven’t created new challenges. Digitisation creates new potential points of failure, sometimes even on top of more traditional security system issues. For example, the increased customisability afforded by the IoT means that bespoke security systems are often a smorgasbord of technologies, protocols, and a variety of devices from multiple vendors. The first challenge security system integrators face is that they need to get all these devices on a secure network, and then ensure each component is configured and optimised to perform as it should and interact with all other devices in the system. This job can take days or even weeks to accomplish. However, system set up is just the tip of the iceberg.
Like all IoT systems, a digitised security is only as strong as the network it is hosted on. Bottlenecks, bandwidth issues, or routing problems that prevent data being sent or received properly can all lead to physical security breaches going undetected.
Nonetheless, it’s not just physical criminals those in charge of security systems have to be wary of. All connected security systems are potentially hackable. A cybercriminal with access to the network can have the power to shut down the security system entirely or use connected devices for nefarious purposes.
Ensuring peak performance
Although the risks cannot be entirely avoided; device malfunction and network failure can and do happen to even the most meticulously set up systems. The good news is there are clear and simple preventative steps security staff can take to ensure their digitised security system operates at peak performance with minimal downtime. Just like a security system monitors a physical location to keep it secure and operational. Digitised security systems must be monitored so at any time staff can see whether there are any issues on the network that need to be addressed. This way problems can be solved proactively, often before any downtime can occur.
Visibility is everything
The same general steps that apply to monitoring traditional IT environments also apply to monitoring a security system network. First the admin in charge of the security system needs to establish the metrics that define a healthy system. For example; they must work out how much bandwidth specific devices use when operating normally, define normal traffic flow across key areas of the network at different times of day, as well as set limits for standard CPU usage for servers and storage systems.
Once all key metrics for each component are defined, this can be input into a specialist monitoring system in order to set up thresholds. This way the monitoring solution knows to alert admins to abnormal readings that may indicate a problem. Only with a monitoring system in place is it possible for admins to get a clear view of the entire network at any one time. Not only does this help to minimise downtime, it also gives admins a component by component view of the system that can help to make adjustments to continually track and improve security system performance.
Digitised security systems are here to stay. With the correct management systems in place they can help us stay secure whilst offering a wealth of benefits for businesses and staff. To keep us safe, we must monitor to master.