A report aggregating insight from more then 400 interviews with leading cybersecurity researchers and security experts on Artificial Intelligence (AI), Machine Learning (ML) and Non-Malware Attacks has found that 87 per cent of those polled still don’t trust AI or ML to replace human decision making in security.
Commissioned by endpoint security specialists Carbon Black, the report also revealed the following trends:
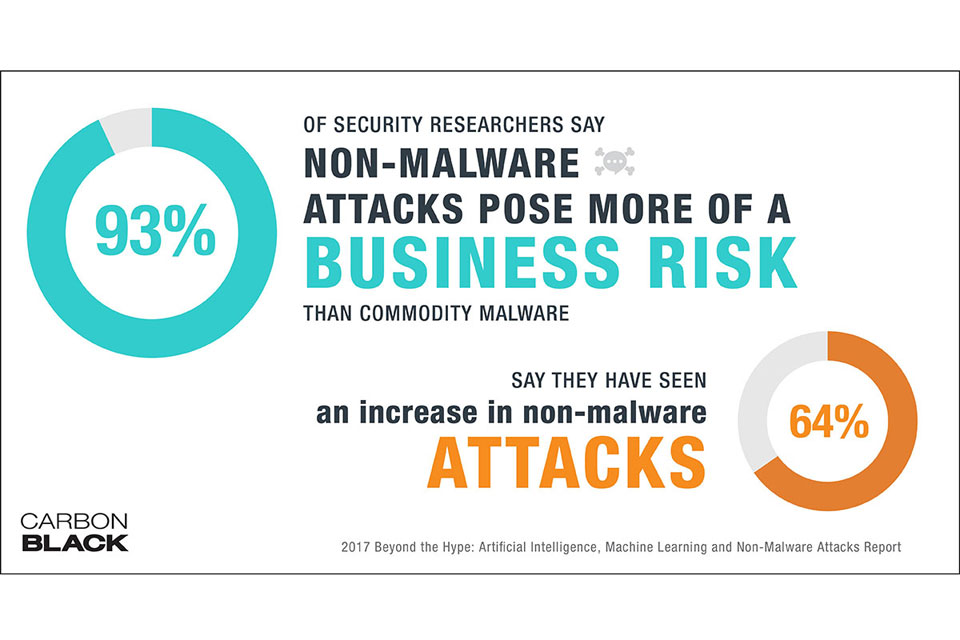
- 93 per cent of cybersecurity researchers said non-malware attacks pose more of a business risk than commodity malware attacks.
- 64 per cent of cybersecurity researchers said they’ve seen an increase in non-malware attacks since the beginning of 2016. There non-malware attacks are increasingly leveraging native system tools, such as WMI and PowerShell, to conduct nefarious actions, researchers reported.
- AI is considered by most cybersecurity researchers to be in its nascent stages and not yet able to replace human decision making in cybersecurity. 87 per cent of the researchers said it will be longer than three years before they trust AI to lead cybersecurity decisions.
- 74 per cent of researchers said AI-driven cybersecurity solutions are still flawed.
- 70 per cent of cybersecurity researchers said ML-driven security solutions can be bypassed by attackers. 30 per cent said attackers could “easily” bypass ML-driven security.
- Cybersecurity talent, resourcing and trust in executives continue to be top challenges plaguing many businesses.
“Based on how cybersecurity researchers perceive current AI-driven security solutions, cybersecurity is still very much a ‘human vs. human’ battle, even with the increased levels of automation seen on both the offensive and defensive sides of the battlefield,” said Carbon Black Co-founder and Chief Technology Officer, Michael Viscuso. “And, the fault with machine learning exists in how much emphasis organisations may be placing on it and how they are using it. Static, analysis-based approaches relying exclusively on files have historically been popular, but they have not proven sufficient for reliably detecting new attacks. Rather, the most resilient ML approaches involve dynamic analysis – evaluating programmes based on the actions they take.”
In addition to key statistics from the research, the report also includes a timeline of notable non-malware attacks, recommendations for incorporating AI and ML into cybersecurity programs and an ‘In Their Own Words’ section, which includes direct quotes from cybersecurity researchers and unique perspectives on the evolution of non-malware attacks.
“Non-malware attacks will become so widespread and target even the smallest business that users will become familiar with them,” said one cybersecurity researcher. “Most users seem to be familiar with the idea that their computer or network may have accidentally become infected with a virus, but rarely consider a person who is actually attacking them in a more proactive and targeted manner.”