Solink: Transforming High Street retail with AI-Driven Video Intelligence

We all know the pressure today’s high street retailers are under; between soaring labor costs and the rise in retail crime, protecting your margin has never been harder. Solink is designed to take that weight off your store teams, and arm your operators to drive results. By layering AI over your existing video and data […]
INDUSTRY SPOTLIGHT: Arcules – Video Surveillance without the complexity
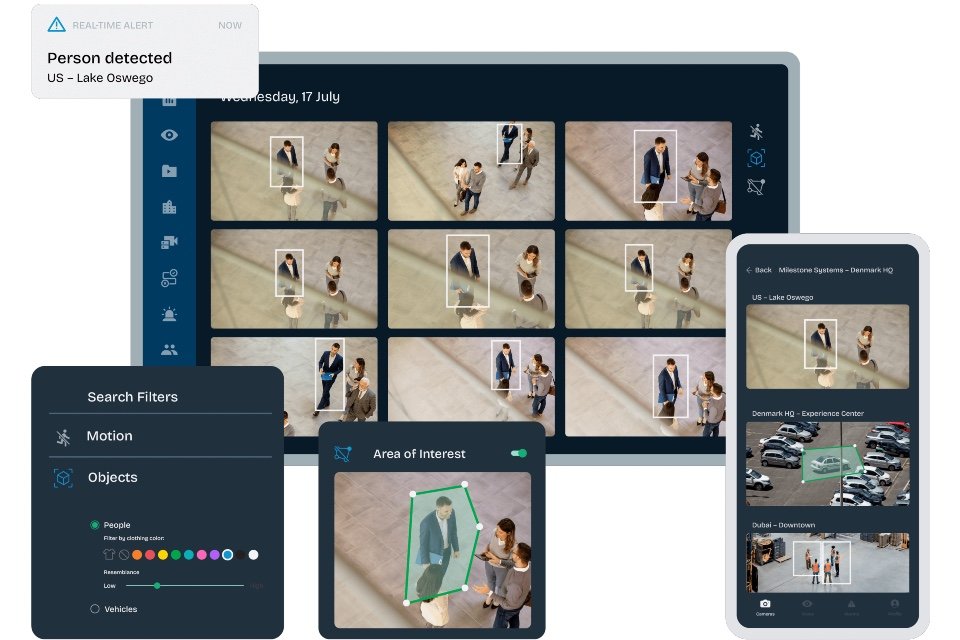
Some organisations need a security system that’s easy to use and affordable to deploy. Arcules meets this need with cloud-based video surveillance as a service (VSaaS). The ease of installation and accessibility of Arcules is ideal for remotely monitoring sites with minimal staff and IT resources. Ensure simple, secure coverage Access live and recorded video […]
INDUSTRY GUIDE: Choosing the best VSaaS for your organisation

This blog explains what VSaaS is, what its benefits are and who can benefit the most from its implementation, as well as provides a checklist of the most important questions to consider when looking for a provider. What is VSaaS? VSaaS (short for video surveillance as a service) allows you to record, monitor, manage, play […]
Gen Z doesn’t like bodycams on security staff, but still changes behaviour in positive way

Nearly one in three (29%) young adults aged 18–24 in the UK say they feel uncomfortable when retail or security staff wear body-worn cameras, despite being digital natives. That’s according to research from body-worn camera company, HALOS. Its YouGov survey of over 2,200 Brits also found that more than a quarter (26%) of those aged 25–34 feel uneasy […]
SURVEILLANCE & MONITORING MONTH: Integrating your surveillance needs into unified Security Operations Centres

The future of security infrastructure is being defined by convergence. Security Operations Centres (SOCs) are no longer siloed hubs of disparate systems. Instead, forward-thinking organisations attending the Total Security Summit in both public and private sectors are adopting unified SOC platforms, integrating surveillance, access control, and intrusion detection into a single, cohesive operational environment… At […]
SURVEILLANCE MONTH: Watching over Britain – How public and private sector surveillance has evolved

The landscape of surveillance & monitoring in the UK has undergone a significant transformation in recent years. Driven by advancements in technology, growing security concerns, and evolving legal frameworks, organisations in both the public and private sectors are re-evaluating their approaches to security monitoring. Let’s delve into this evolving landscape and explore how solutions for senior physical security professionals are […]
CCTV MONTH: Answering the rise in security threats with better communication and surveillance

Police recorded crime in England and Wales in the year ending December 2022 exceeded pre-coronavirus pandemic levels. The number of professional security guards in the UK is on the decline, and it is widely known that the sector is having a challenging time recruiting for a shortage of staff. Additionally, people employed within the professional […]
CCTV MONTH: The evolution of CCTV in commercial security – A decade of transformation

Closed-Circuit Television (CCTV) has long been a cornerstone of commercial security. Over the past decade, however, the capabilities and functions of CCTV systems have evolved tremendously, driven by technological advancements and the changing needs of businesses. Let’s dive into the key developments that have shaped the world of commercial CCTV in the past ten years, […]
Hosted physical security adoption given ‘major boost’ by uptake in cloud

New research into the impact of COVID-19 on physical security purchasing decisions has revealed a sharp increase in the necessity/urgency for businesses to adopt hosted video surveillance (VSaaS) and access control (ACaaS) solutions. While 70% of 1000 senior decision makers in IT, security, FM and HR roles agree this to be the case, 78% also anticipate their organisations’ […]
Number of CCTV Cameras in the UK reaches 5.2 million

The number of CCTV Cameras in the UK may be as many as 5.2 million, with 1 camera for every 13 people as the popularity of public surveillance, home CCTV and doorbell camera use increases. That’s according to research, which says 96% of the total number of cameras in the UK are now operated by […]
