AI in Cybersecurity: Small business owners urged to shift from fear to smart governance

As AI becomes more deeply embedded in everyday business tools and workflows, small business owners are being urged to rethink their approach to cybersecurity. Rather than attempting to avoid AI, experts advise that businesses should embrace it while implementing strong governance and security practices. Here, Marko Antonić, Cloud Workspace Engineer, from Haypp, shares his advice for business owners […]
MOBILE IDS, MFA AND SUSTAINABILITY EMERGE AS TOP SECURITY TRENDS, SAYS NEW REPORT

HID’s 2024 State of the Security Industry Report has outlined the underlying concerns driving upcoming innovations and the technologies that underpin them, including Mobile IDs, MFA and sustainability. The report gathered responses from 2,600 partners, end users, and security and IT personnel worldwide, across a range of job titles and organisation sizes representing over 11 […]
Six disruptive trends that will shape physical security in the next five years

Physical security is on the cusp of significant change, driven by a confluence of technological advancements and evolving threats. In the coming five years, several disruptive trends are poised to reshape how physical security is managed, offering both challenges and opportunities for businesses and security professionals. Here are the key trends and their potential impact […]
From AI to ESG: Key security-technology trends of 2023

Johan Paulsson, Chief Technology Officer, Axis Communications, explores the six key technology trends that are set to impact the security sector in the coming year… Technology is pervasive in every aspect of our personal and work lives. Every new technological development and every upgrade brings new benefits, makes the tools we rely on more effective, […]
5 Minutes With… Hanwha Techwin’s Billy Hopkins

In the latest instalment of our security industry executive interview series we spoke to Billy Hopkins (pictured, right), National Account Manager at Hanwha Techwin, about the company, the ongoing challenges of COVID-19 for the security sector, cyber security in video surveillance, the impact of AI and more… Tell us about your company, products and services. Hanwha […]
F24 and The BCI present the new Emergency Communications Report 2021

The pandemic has driven organisations to adopt collaboration software in 2020 and this trend is expected to continue for 2021. Previous reports have highlighted an overreliance on tools from the private environment for communication during emergency situations (e.g. WhatsApp). Organisations are moving away from tools from such as WhatsApp and using more collaborative tools such […]
Five top technology trends set to impact the security sector in 2020

As existing technologies reach maturity and innovations make the leap from consumer applications to business (and vice versa), it’s imperative that we constantly seek to find those that have the potential to add value to our own business and those of our customers. As we look ahead to 2020, Johan Paulsson, CTO, Axis Communications has […]
Industry Spotlight: Gallagher releases latest mobile security technology to international market
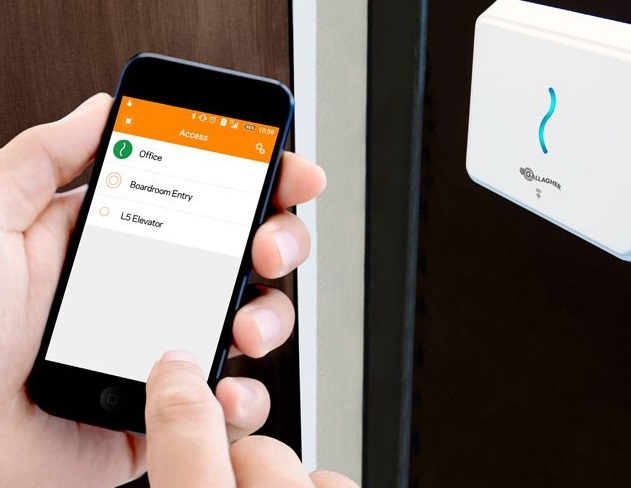
Gallagher has released its latest state-of-the-art mobile security solution: Gallagher Mobile Connect. Mobile Connect transforms a mobile phone in to an access device, using FIDO certified authentication to deliver exceptionally safe and secure credentials – empowering businesses to use mobile technology in place of traditional access cards. Delivering more than just peace-of-mind, Gallagher’s new mobile […]
Apple delays app transport security deadline

Apple has backtracked on its plan to enforce a year-end deadline for 2016 that would have required developers to move apps to an HTTPS-only model in an effort to thwart eavesdropping on insecure, plaintext HTTP connections. In a short statement at the end of last month, Apple said that a requirement for developers to adopt […]
Gallagher launches new mobile security app to international market…

Gallagher has announced the release of its Mobile Connect app which promises to transform a mobile phone into an access device – empowering businesses to use mobile technology in place of traditional access cards. The security division of the Gallagher Group partnered with the FIDO (Fast IDentity Online) Alliance and Nok Nok Labs to create the app, which uses two-step remote provisioning to deliver secure enrolment by sending […]
